The malicious apps reached an astonishing spread between 4.5 million and 18.5 million downloads.
Almost 36.5 million Android devices have been affected with a new malware dubbed ‘Judy’. It has been found in 41 apps on the Google Play Store, and uses infected devices to generate fraudulent clicks on advertisements, generating revenues for the perpetrators behind it.
According to Check Point, some of the apps discovered resided on Google Play for several years, but all were recently updated. It is unclear how long the malicious code existed inside the apps, hence the actual spread of the malware remains unknown. The security firm also stated that the malicious apps reached an astonishing spread between 4.5 million and 18.5 million downloads.
Similar to previous malware which infiltrated Google Play, such as FalseGuide and Skinner, Judy reportedly relies on the communication with its Command and Control server (C&C) for its operation. After the firm alerted Google, the apps were removed from the Play store.
How does the Judy Malware work?
To bypass Bouncer, Google Play’s protection, the hackers create a seemingly benign bridgehead app, meant to establish connection to the victim’s device, and insert it into the app store. Once a user downloads a malicious app, it silently registers receivers which establish a connection with the C&C server. The server replies with the actual malicious payload, which includes JavaScript code, a user-agent string and URLs controlled by the malware author.
The malware opens the URLs using the user agent that imitates a PC browser in a hidden webpage and receives a redirection to another website. Once the targeted website is launched, the malware uses the JavaScript code to locate and click on banners from the Google ads infrastructure. Upon clicking the ads, the malware author receives payment from the website developer, which pays for the illegitimate clicks and traffic.
But, who is behind the Judy Malware?
CheckPoint stated that the malicious apps are all developed by a Korean company named Kiniwini, registered on Google Play as ENISTUDIO corp. The company develops mobile apps for both Android and iOS platforms. It is quite unusual to find an actual organization behind mobile malware, as most of them are developed by purely malicious actors. It is important to note that the activity conducted by the malware is not borderline advertising, but definitely an illegitimate use of the users’ mobile devices for generating fraudulent clicks, benefiting the attackers.
Mentioned below is the list of malicious apps released by Check Point:
Fashion Judy: Snow Queen style
Animal Judy: Persian cat care
Fashion Judy: Pretty rapper
Fashion Judy: Teacher style
Animal Judy: Dragon care
Chef Judy: Halloween Cookies
Fashion Judy: Wedding Party
Animal Judy: Teddy Bear care
Fashion Judy: Bunny Girl Style
Fashion Judy: Frozen Princess
Chef Judy: Triangular Kimbap
Chef Judy: Udong Maker – Cook
Fashion Judy: Uniform style
Animal Judy: Rabbit care
Fashion Judy: Vampire style
Animal Judy: Nine-Tailed Fox
Chef Judy: Jelly Maker – Cook
Chef Judy: Chicken Maker
Animal Judy: Sea otter care
Animal Judy: Elephant care
Judy’s Happy House
Chef Judy: Hotdog Maker – Cook
Chef Judy: Birthday Food Maker
Fashion Judy: Wedding day
Fashion Judy: Waitress style
Chef Judy: Character Lunch
Chef Judy: Picnic Lunch Maker
Animal Judy: Rudolph care
Judy’s Hospital: Pediatrics
Fashion Judy: Country style
Animal Judy: Feral Cat care
Fashion Judy: Twice Style
Fashion Judy: Myth Style
Animal Judy: Fennec Fox care
Animal Judy: Dog care
Fashion Judy: Couple Style
Animal Judy: Cat care
Fashion Judy: Halloween style
Fashion Judy: EXO Style
Chef Judy: Dalgona Maker
Chef Judy: ServiceStation Food
Judy’s Spa Salon
![submenu-img]() US imposes sanctions on Chinese, Belarus firms for providing ballistic missile tech to Pakistan
US imposes sanctions on Chinese, Belarus firms for providing ballistic missile tech to Pakistan![submenu-img]() 'Don't have any comment': White House mum on reports of Israeli strikes in Iran
'Don't have any comment': White House mum on reports of Israeli strikes in Iran![submenu-img]() Yes Bank co-founder Rana Kapoor gets bail after four years in bank fraud case
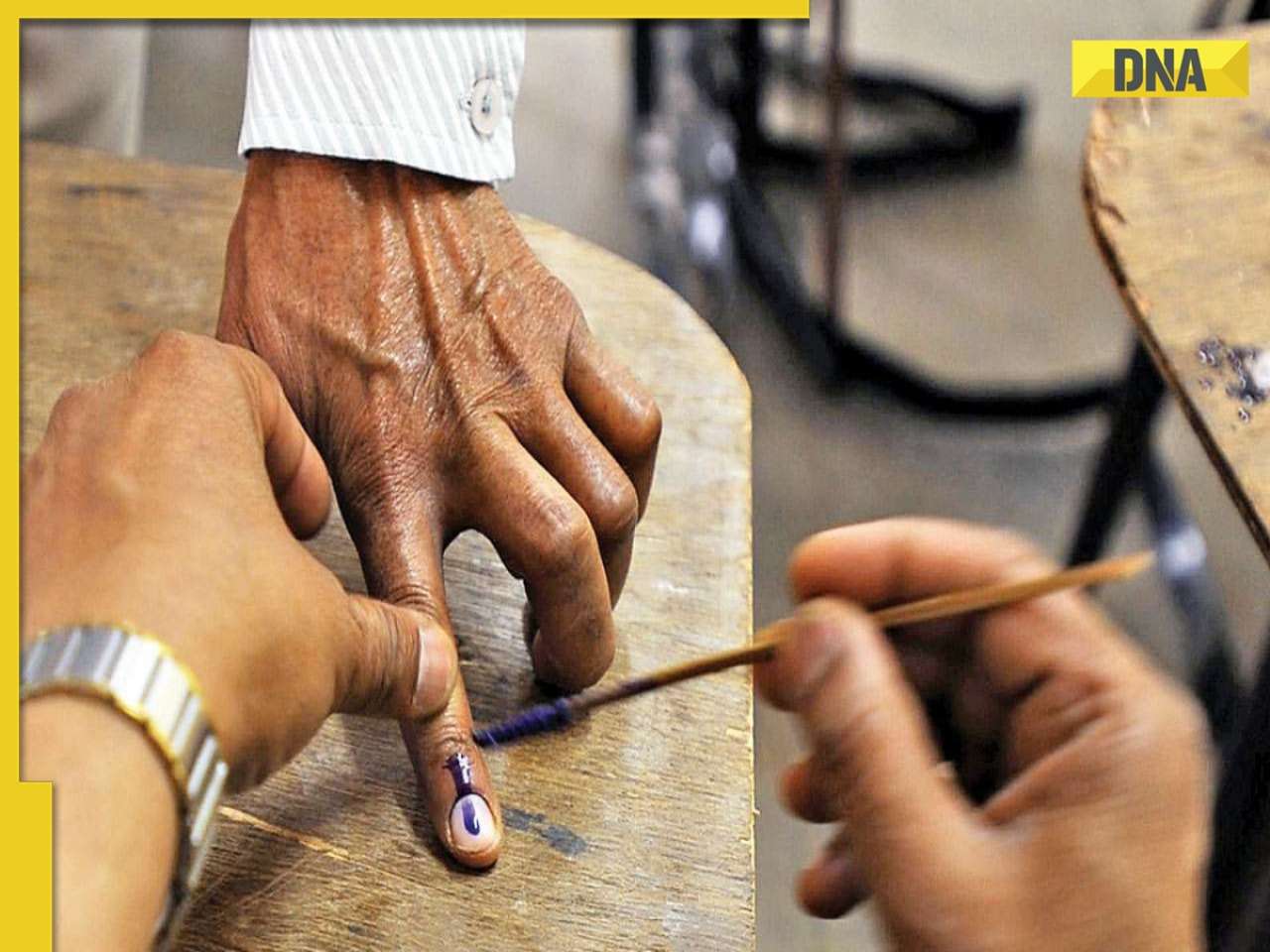
Yes Bank co-founder Rana Kapoor gets bail after four years in bank fraud case![submenu-img]() Barmer Lok Sabha Polls 2024: Check key candidates, date of voting and other important details
Barmer Lok Sabha Polls 2024: Check key candidates, date of voting and other important details![submenu-img]() This star once lived in garage, earned Rs 51 as first salary; now charges Rs 5 crore per film, is worth Rs 335 crore
This star once lived in garage, earned Rs 51 as first salary; now charges Rs 5 crore per film, is worth Rs 335 crore![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
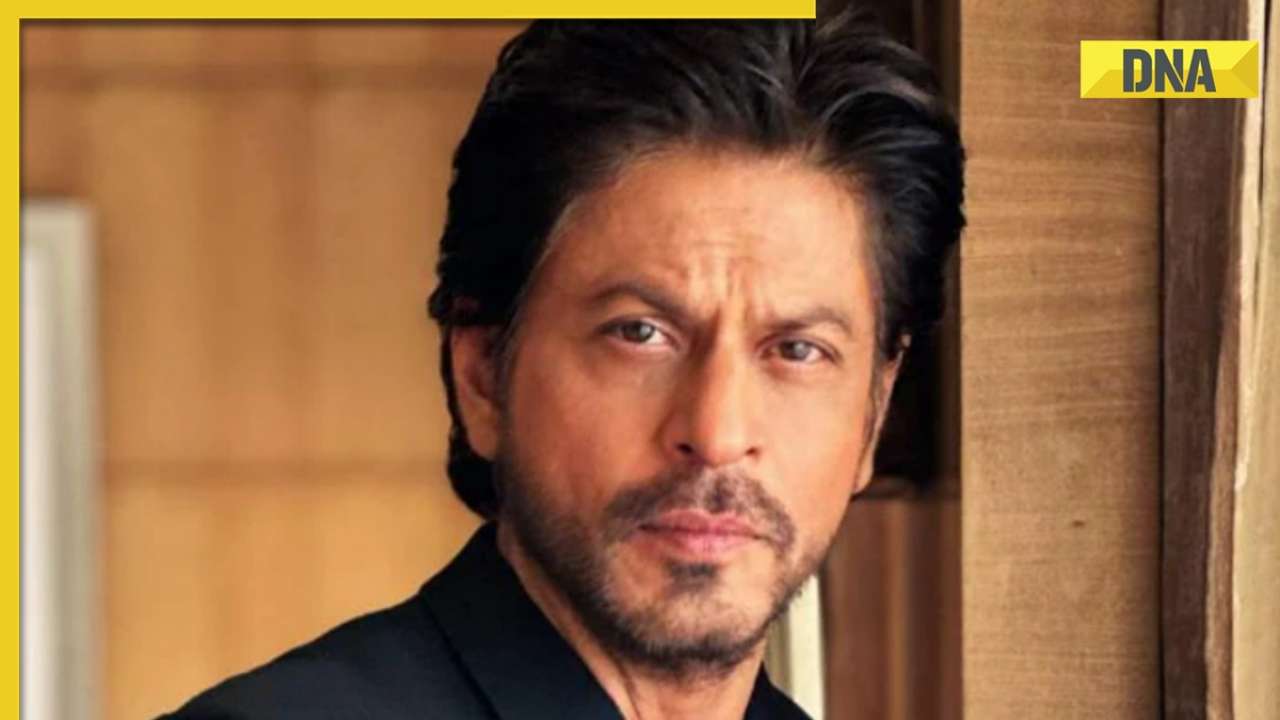
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
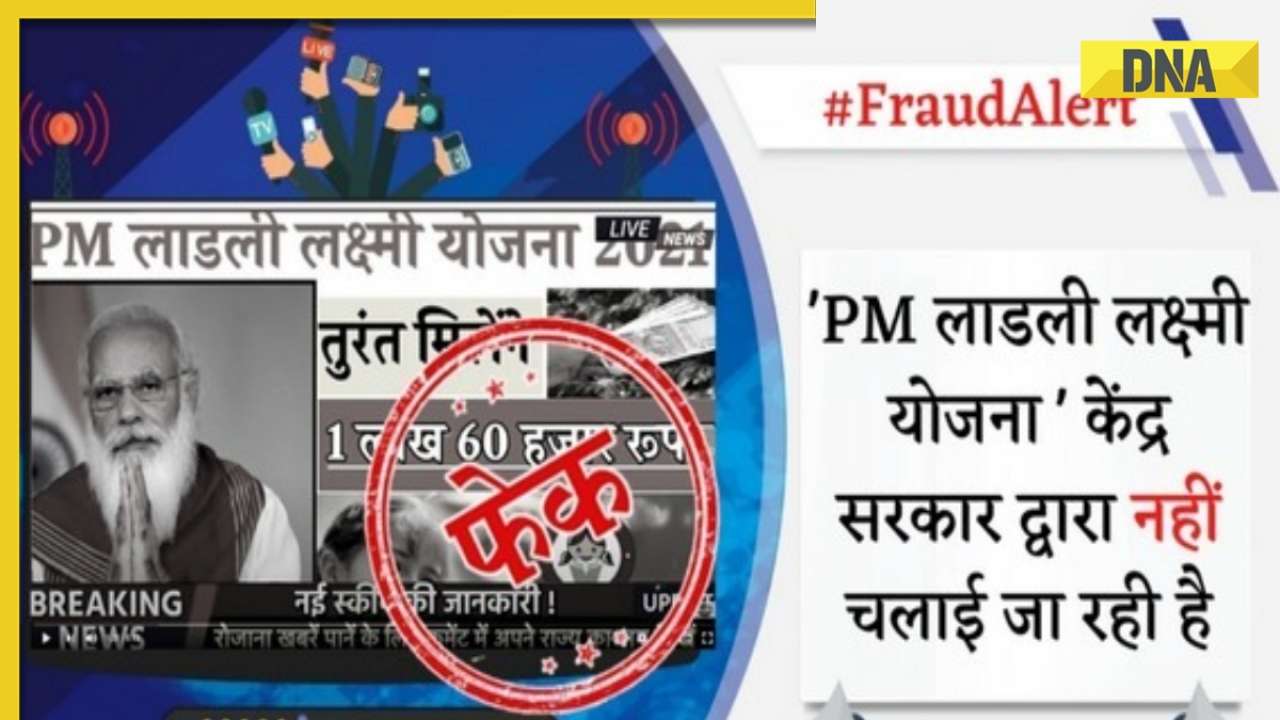
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now
Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now![submenu-img]() Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..
Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..![submenu-img]() In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding
In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding![submenu-img]() In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month
In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month![submenu-img]() Remember Jibraan Khan? Shah Rukh's son in Kabhi Khushi Kabhie Gham, who worked in Brahmastra; here’s how he looks now
Remember Jibraan Khan? Shah Rukh's son in Kabhi Khushi Kabhie Gham, who worked in Brahmastra; here’s how he looks now![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles
DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles![submenu-img]() This star once lived in garage, earned Rs 51 as first salary; now charges Rs 5 crore per film, is worth Rs 335 crore
This star once lived in garage, earned Rs 51 as first salary; now charges Rs 5 crore per film, is worth Rs 335 crore![submenu-img]() Meet actress, who worked as cook for free food, mopped floors, one Instagram post changed her life, is now worth…
Meet actress, who worked as cook for free food, mopped floors, one Instagram post changed her life, is now worth… ![submenu-img]() UP man arrested for booking cab from Salman Khan's house under Lawrence Bishnoi's name
UP man arrested for booking cab from Salman Khan's house under Lawrence Bishnoi's name ![submenu-img]() 'Justice milega': Ankita Lokhande talks about Sushant Singh Rajput, reveals she's still connected with his family
'Justice milega': Ankita Lokhande talks about Sushant Singh Rajput, reveals she's still connected with his family![submenu-img]() Rajkummar Rao reacts to plastic surgery rumours, admits he got fillers: 'If something gives me confidence...'
Rajkummar Rao reacts to plastic surgery rumours, admits he got fillers: 'If something gives me confidence...'![submenu-img]() IPL 2024: KL Rahul, Quinton de Kock star in Lucknow Super Giants' dominating 8-wicket win over Chennai Super Kings
IPL 2024: KL Rahul, Quinton de Kock star in Lucknow Super Giants' dominating 8-wicket win over Chennai Super Kings![submenu-img]() DC vs SRH, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
DC vs SRH, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() Watch: Virat Kohli's cheeky 'your wife' remark to Dinesh Karthik leaves RCB teammates in splits
Watch: Virat Kohli's cheeky 'your wife' remark to Dinesh Karthik leaves RCB teammates in splits ![submenu-img]() DC vs SRH IPL 2024 Dream11 prediction: Fantasy cricket tips for Delhi Capitals vs Sunrisers Hyderabad
DC vs SRH IPL 2024 Dream11 prediction: Fantasy cricket tips for Delhi Capitals vs Sunrisers Hyderabad![submenu-img]() 'Kohli said it's not an option, just...': KL Rahul recalls his IPL debut for RCB in 2013
'Kohli said it's not an option, just...': KL Rahul recalls his IPL debut for RCB in 2013![submenu-img]() Canada's biggest heist: Two Indian-origin men among six arrested for Rs 1300 crore cash, gold theft
Canada's biggest heist: Two Indian-origin men among six arrested for Rs 1300 crore cash, gold theft![submenu-img]() Donuru Ananya Reddy, who secured AIR 3 in UPSC CSE 2023, calls Virat Kohli her inspiration, says…
Donuru Ananya Reddy, who secured AIR 3 in UPSC CSE 2023, calls Virat Kohli her inspiration, says…![submenu-img]() Nestle getting children addicted to sugar, Cerelac contains 3 grams of sugar per serving in India but not in…
Nestle getting children addicted to sugar, Cerelac contains 3 grams of sugar per serving in India but not in…![submenu-img]() Viral video: Woman enters crowded Delhi bus wearing bikini, makes obscene gesture at passenger, watch
Viral video: Woman enters crowded Delhi bus wearing bikini, makes obscene gesture at passenger, watch![submenu-img]() This Swiss Alps wedding outshine Mukesh Ambani's son Anant Ambani's Jamnagar pre-wedding gala
This Swiss Alps wedding outshine Mukesh Ambani's son Anant Ambani's Jamnagar pre-wedding gala






























)




)
)
)
)
)
)