Security researchers with Google Inc and a small Finnish security firm Codenomicon have discovered a serious vulnerability in OpenSSL, the cryptographic software library that protects most of the Internet. They have called this vulnerability the HeartBleed bug, which has been present for over two years. HeartBleed has given a major scare to people in connection with the protection of passwords, credit card numbers and other information that may be at risk.
Security expert Bruce Schneier calls Heartbleed a catastrophic vulnerability. "On the scale of 1 to 10, this is an 11. Half a million sites are vulnerable, including my own," he wrote in his blog post.
Kurt Baumgartner, researcher with Kaspersky Lab, a privately held vendor of endpoint protection solutions, says the lab uncovered evidence that a few hacking groups believed to be involved in state-sponsored cyber espionage were running such scans. "Our team identified such scans. The numbers were gradually increasing and this was even more evident when security software company Rapid7 released a free tool for conducting such scans. This problem is insidious and devices besides servers could be at risk because they run software programmes with vulnerable OpenSSL code built into them."
Ever since Edward Snowden exposed the National Security Agency's (NSA's) widespread efforts to eavesdrop on the Internet, people looked at encryption as the answer to their problem. Encryption is a method which allows information like a secret message to be hidden so that it cannot be read without special knowledge (like a password). Snowden gave the hope that encryption is a saving grace in the face of NSA's snooping. "Encryption works," the whistleblower said last June. "Properly implemented strong crypto systems are one of the few things that you can rely on."
Snowden also warned that crypto systems aren't always properly implemented. "Unfortunately," he said, "endpoint security is so terrifically weak that NSA can frequently find ways around it." The bigger question is the one that even security expert Bruce Schnier repeated. "The real question is whether or not someone deliberately inserted this bug into OpenSSL, and has had two years of unfettered access to everything."
The problem lies with the fact that most of the websites in the world rely on a tiny group of poorly paid programmers to keep you safe from hackers.
For all the people who own websites that use OpenSSL, the bug has been patched. After you patch your systems, you have to get a new public/private key pair, update your SSL certificate, and then change every password that could potentially be affected. For all internet users, the safest option would be to change all passwords.
If major web companies pitch in for regular audits of OpenSSL's code, an incident like this can be easily avoided. The hope is that people who use open source software will take auditing it more seriously and reveal the audit results publicly so that the lesser fortunate firms and individuals can stay secure as well. -With inputs from Priyanka Golikeri
What are sites doing
Facebook: Unclear if it was affected, but site has deployed a patch so you can change your password
Twitter: Company yet to comment. It's better not use a password common with other services
Google: It said users do not need to change passwords for accessing Gmail, YouTube
Tumblr/Flickr: Has fixed the problem. You must change its password immediately
Yahoo: It has deployed patches on major services but others remain. It is advising users to rotate passwords
Hotamail/Outlook/LinkedIn/Microsoft Services not affected; Amazon.com Inc says websites weren't exposed to Heartbleed
![submenu-img]() Explainer: Why Spain's PM Pedro Sanchez is taking break from public duties?
Explainer: Why Spain's PM Pedro Sanchez is taking break from public duties?![submenu-img]() Meet superstar who was made to kiss 10 men during audition, feared being called 'difficult', net worth is..
Meet superstar who was made to kiss 10 men during audition, feared being called 'difficult', net worth is..![submenu-img]() Mukesh Ambani's Reliance makes big announcement, unveils new free…
Mukesh Ambani's Reliance makes big announcement, unveils new free…![submenu-img]() Secret Service agent protecting US Vice President Kamala Harris removed after brawl with other officers
Secret Service agent protecting US Vice President Kamala Harris removed after brawl with other officers![submenu-img]() Who is Iranian rapper Toomaj Salehi, why is he sentenced to death? Know on what charges
Who is Iranian rapper Toomaj Salehi, why is he sentenced to death? Know on what charges![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
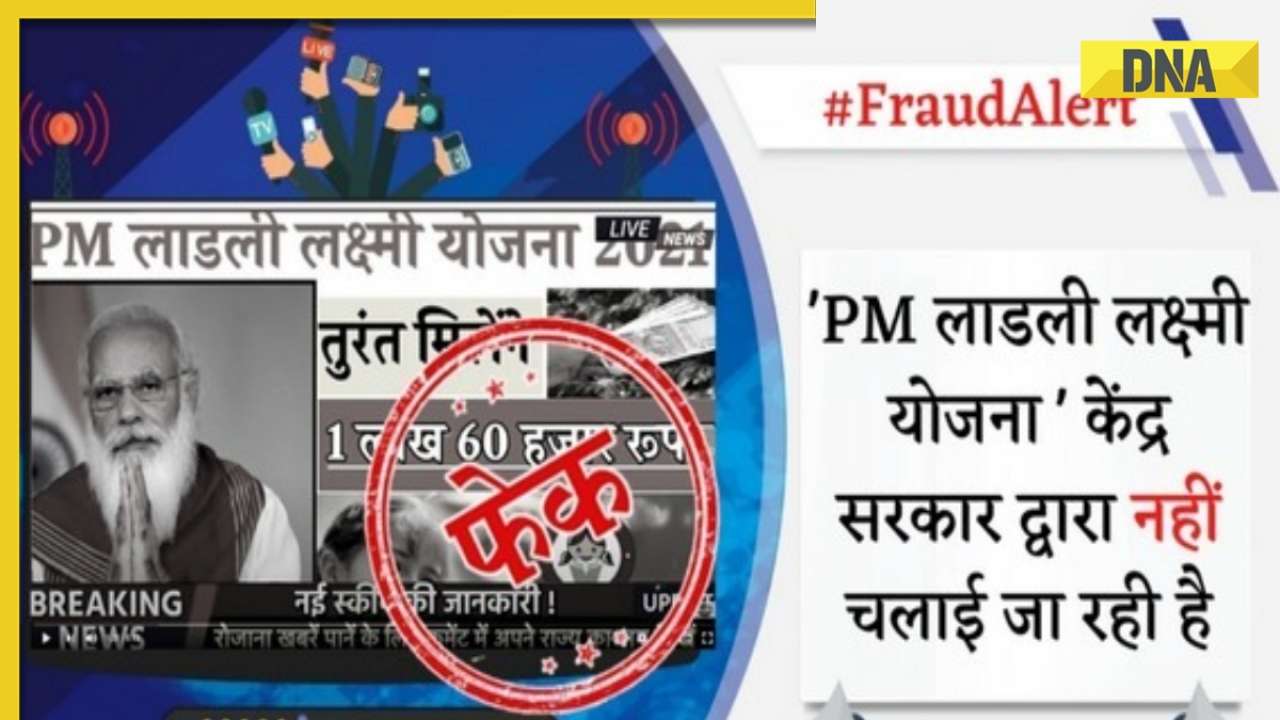
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() In pics: Salman Khan, Alia Bhatt, Rekha, Neetu Kapoor attend grand premiere of Sanjay Leela Bhansali's Heeramandi
In pics: Salman Khan, Alia Bhatt, Rekha, Neetu Kapoor attend grand premiere of Sanjay Leela Bhansali's Heeramandi![submenu-img]() Streaming This Week: Crakk, Tillu Square, Ranneeti, Dil Dosti Dilemma, latest OTT releases to binge-watch
Streaming This Week: Crakk, Tillu Square, Ranneeti, Dil Dosti Dilemma, latest OTT releases to binge-watch![submenu-img]() From Salman Khan to Shah Rukh Khan: Actors who de-aged for films before Amitabh Bachchan in Kalki 2898 AD
From Salman Khan to Shah Rukh Khan: Actors who de-aged for films before Amitabh Bachchan in Kalki 2898 AD![submenu-img]() Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..
Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..![submenu-img]() Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now
Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now![submenu-img]() What is inheritance tax?
What is inheritance tax?![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() Meet superstar who was made to kiss 10 men during audition, feared being called 'difficult', net worth is..
Meet superstar who was made to kiss 10 men during audition, feared being called 'difficult', net worth is..![submenu-img]() Lara Dutta has this to say about trolls calling her ‘buddhi, moti’: ‘I don’t know what someone like that…’
Lara Dutta has this to say about trolls calling her ‘buddhi, moti’: ‘I don’t know what someone like that…’![submenu-img]() Meet actress, who gave first Rs 100-crore Tamil film; and it’s not Anushka Shetty, Nayanthara, Jyotika, or Trisha
Meet actress, who gave first Rs 100-crore Tamil film; and it’s not Anushka Shetty, Nayanthara, Jyotika, or Trisha ![submenu-img]() Meet actor, school dropout, who worked as mechanic, salesman, later became star; now earns over Rs 100 crore per film
Meet actor, school dropout, who worked as mechanic, salesman, later became star; now earns over Rs 100 crore per film![submenu-img]() This filmmaker earned Rs 150 as junior artiste, bunked college for work, now heads production house worth crores
This filmmaker earned Rs 150 as junior artiste, bunked college for work, now heads production house worth crores![submenu-img]() IPL 2024: Rishabh Pant, Axar Patel shine as Delhi Capitals beat Gujarat Titans by 4 runs
IPL 2024: Rishabh Pant, Axar Patel shine as Delhi Capitals beat Gujarat Titans by 4 runs![submenu-img]() SRH vs RCB, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
SRH vs RCB, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() SRH vs RCB IPL 2024 Dream11 prediction: Fantasy cricket tips for Sunrisers Hyderabad vs Royal Challengers Bengaluru
SRH vs RCB IPL 2024 Dream11 prediction: Fantasy cricket tips for Sunrisers Hyderabad vs Royal Challengers Bengaluru ![submenu-img]() Meet India cricketer who wanted to be IPS officer, got entry in IPL by luck, now earns more than CSK star Dhoni, he is..
Meet India cricketer who wanted to be IPS officer, got entry in IPL by luck, now earns more than CSK star Dhoni, he is..![submenu-img]() IPL 2024: Marcus Stoinis' century power LSG to 6-wicket win over CSK
IPL 2024: Marcus Stoinis' century power LSG to 6-wicket win over CSK![submenu-img]() Viral video: Truck driver's innovative solution to beat the heat impresses internet, watch
Viral video: Truck driver's innovative solution to beat the heat impresses internet, watch![submenu-img]() 'Look between E and Y on your keyboard': All you need to know about new 'X' trend
'Look between E and Y on your keyboard': All you need to know about new 'X' trend![submenu-img]() Watch: Pet dog scares off alligator in viral video, internet reacts
Watch: Pet dog scares off alligator in viral video, internet reacts![submenu-img]() Professional Indian gamers earn unbelievable amounts of money amid gaming boom; Know about their annual earnings
Professional Indian gamers earn unbelievable amounts of money amid gaming boom; Know about their annual earnings![submenu-img]() Meet first Asian woman without arms to get driving licence, she is from...
Meet first Asian woman without arms to get driving licence, she is from...
































)




)
)
)
)
)
)