On Friday, Apple released a major update to patch up a hole in the security of all its products with iOS 7. The flaw which was downplayed by Apple, is arguably one of their biggest lapses in security, exposing iPhone, iPad and iPod Touch users to hackers.
The glitch would allow hackers to intercept email and other forms of online communication that are meant to be encrypted. Experts claim that Mac computers that run on iOS 7 are more vulnerable to this threat.
The hackers could access the information from Apple products by means of an unsecured wireless network or through social media and email sites like Facebook and Gmail.
"It's as bad as you could imagine, that's all I can say," said Johns Hopkins University cryptography professor Matthew Green.
Apple has not released any information about how it detected the security flaw and whether it has been exploited so far.
A statement on its support website said: "The software failed to validate the authenticity of the connection."

Apple released software patches and an update for the current version of iOS for the iPhone, iPad and iTouch. "Without the fix, a hacker could impersonate a protected site and sit in the middle as email or financial data goes between the user and the real site" Green said.
The flaw has also been detected on versions of Mac OSX, which power Apple laptops and desktops. Although a patch to rectify this isn't out yet, Apple is expected to release one shortly.
As reported to Reuters, Dmitri Alperovich, chief technology officer at security firm CrowdStrike Inc. said "the issue is a fundamental bug in Apple's SSL implementation. Adam Langley, a senior engineer at Google, agreed with CrowdStrike that OS X was at risk.
Reuters goes on to report, Apple did not reply to requests for comment. The flaw appears to be in the way that well-understood protocols were implemented, an embarrassing lapse for a company of Apple's stature and technical prowess.
It should also be noted that because hackers will also be studying the patch, they could develop programs to take advantage of the flaw within days or even hours.
(With inputs from Reuters)
![submenu-img]() Meet IIT graduate who designed EVM, worked with Microsoft and Google, he works as…
Meet IIT graduate who designed EVM, worked with Microsoft and Google, he works as…![submenu-img]() Tata Motors planning Rs 8360 crore plant to make luxury cars in India, to set up…
Tata Motors planning Rs 8360 crore plant to make luxury cars in India, to set up…![submenu-img]() Meet man who has bought most expensive property on Bengaluru's 'Billionaire Street', Sudha Murty also...
Meet man who has bought most expensive property on Bengaluru's 'Billionaire Street', Sudha Murty also...![submenu-img]() Israel-Iran news live: Israel conducts air strike in Iran in retaliation to missile attack, says report
Israel-Iran news live: Israel conducts air strike in Iran in retaliation to missile attack, says report![submenu-img]() Neeru Bajwa says Punjabi film industry lacks professionalism: ‘We are not going anywhere until…’
Neeru Bajwa says Punjabi film industry lacks professionalism: ‘We are not going anywhere until…’![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
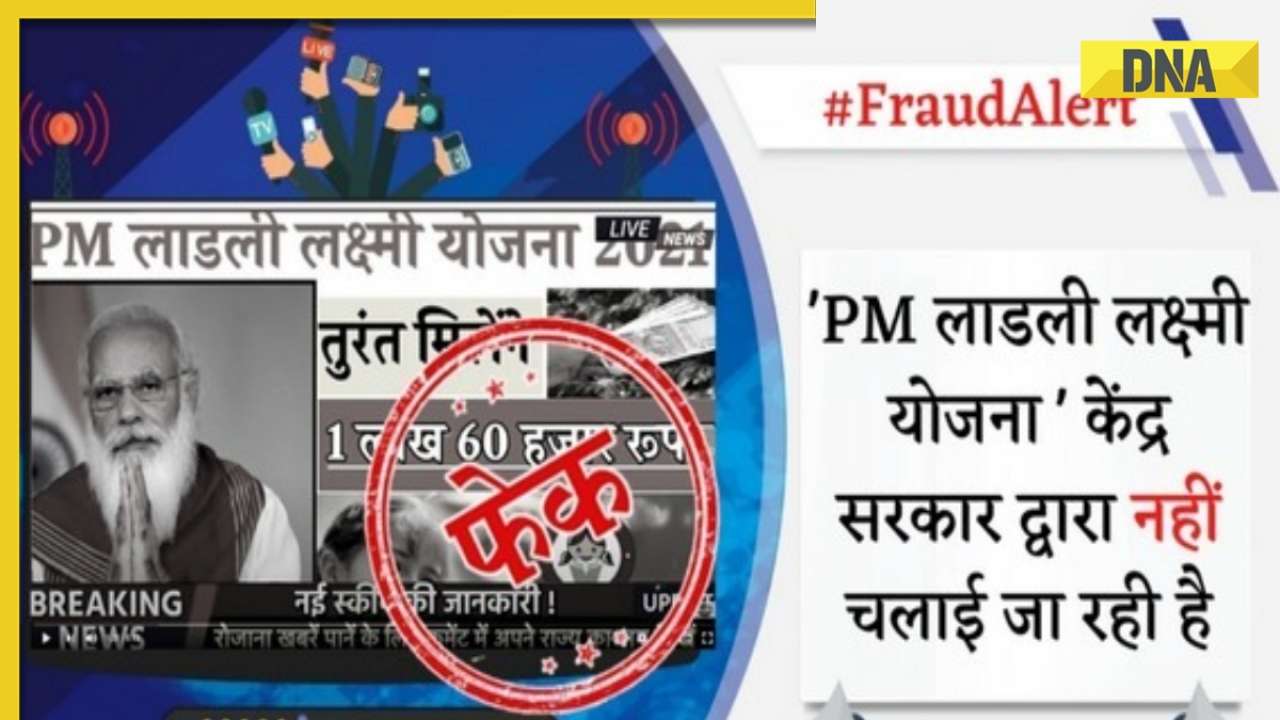
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..
Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..![submenu-img]() In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding
In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding![submenu-img]() In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month
In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month![submenu-img]() Remember Jibraan Khan? Shah Rukh's son in Kabhi Khushi Kabhie Gham, who worked in Brahmastra; here’s how he looks now
Remember Jibraan Khan? Shah Rukh's son in Kabhi Khushi Kabhie Gham, who worked in Brahmastra; here’s how he looks now![submenu-img]() From Bade Miyan Chote Miyan to Aavesham: Indian movies to watch in theatres this weekend
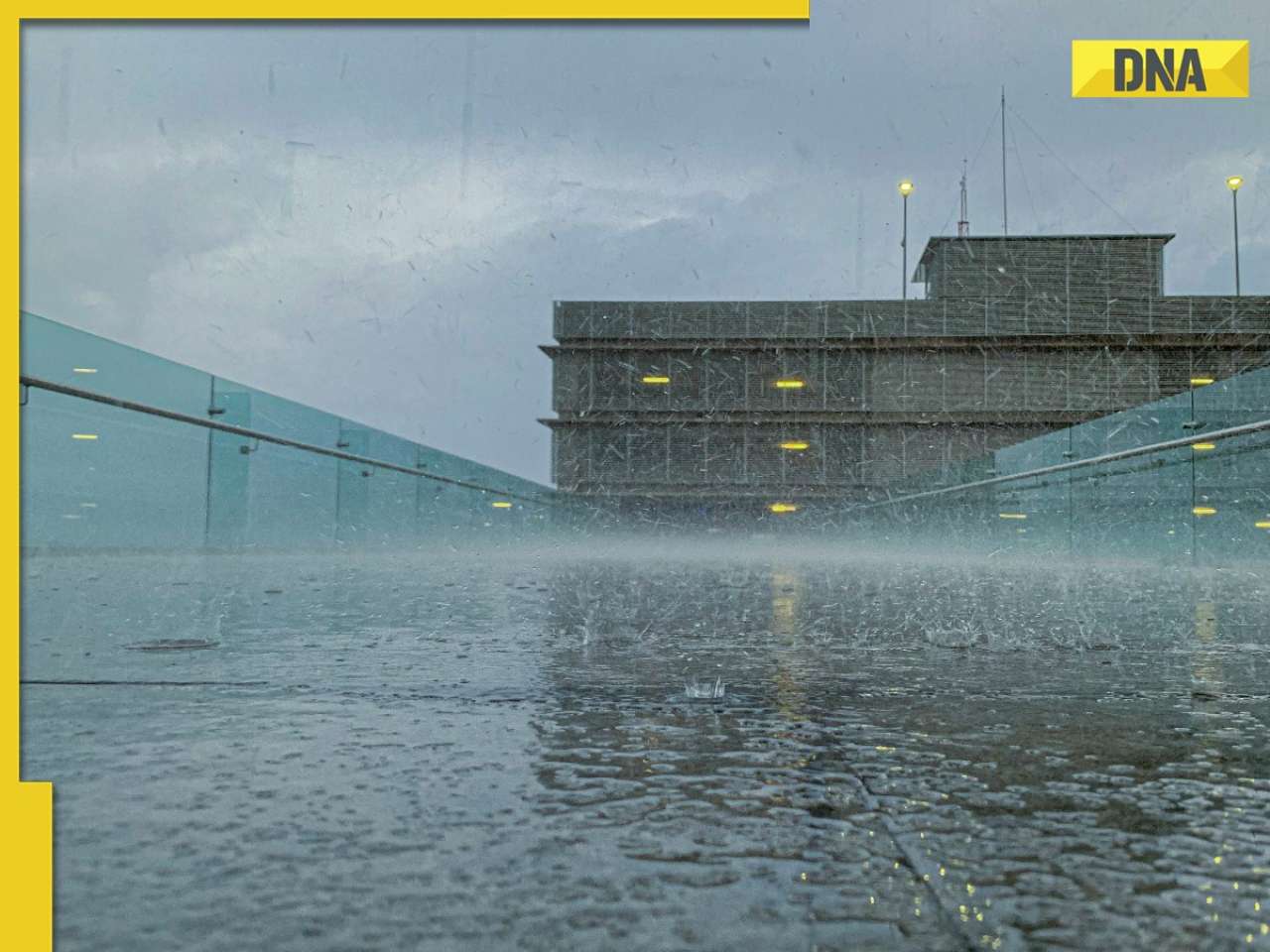
From Bade Miyan Chote Miyan to Aavesham: Indian movies to watch in theatres this weekend ![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles
DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles![submenu-img]() Neeru Bajwa says Punjabi film industry lacks professionalism: ‘We are not going anywhere until…’
Neeru Bajwa says Punjabi film industry lacks professionalism: ‘We are not going anywhere until…’![submenu-img]() Meet actress who married a CM against her family's wishes, became his second wife, her net worth is..
Meet actress who married a CM against her family's wishes, became his second wife, her net worth is..![submenu-img]() Meet India's richest actress, who started career with two flops, was removed from multiple films, is now worth...
Meet India's richest actress, who started career with two flops, was removed from multiple films, is now worth...![submenu-img]() Meet hit director's niece, who was bullied for 15 years, Bollywood debut flopped, will now star in Rs 200 crore project
Meet hit director's niece, who was bullied for 15 years, Bollywood debut flopped, will now star in Rs 200 crore project![submenu-img]() Abhilash Thapliyal discusses Maidaan, reveals he lost chance to play PK Banerjee in Ajay Devgn's film for this reason
Abhilash Thapliyal discusses Maidaan, reveals he lost chance to play PK Banerjee in Ajay Devgn's film for this reason![submenu-img]() IPL 2024: Ashutosh Sharma's heroics in vain as Mumbai Indians return to winning ways with 9-run victory over PBKS
IPL 2024: Ashutosh Sharma's heroics in vain as Mumbai Indians return to winning ways with 9-run victory over PBKS![submenu-img]() LSG vs CSK, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
LSG vs CSK, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() LSG vs CSK IPL 2024 Dream11 prediction: Fantasy cricket tips for Lucknow Super Giants vs Chennai Super Kings
LSG vs CSK IPL 2024 Dream11 prediction: Fantasy cricket tips for Lucknow Super Giants vs Chennai Super Kings![submenu-img]() PBKS vs MI IPL 2024: Rohit Sharma equals MS Dhoni's massive record, becomes 2nd player to....
PBKS vs MI IPL 2024: Rohit Sharma equals MS Dhoni's massive record, becomes 2nd player to....![submenu-img]() Major setback for CSK as star player ruled out of IPL 2024, replacement announced
Major setback for CSK as star player ruled out of IPL 2024, replacement announced![submenu-img]() Canada's biggest heist: Two Indian-origin men among six arrested for Rs 1300 crore cash, gold theft
Canada's biggest heist: Two Indian-origin men among six arrested for Rs 1300 crore cash, gold theft![submenu-img]() Donuru Ananya Reddy, who secured AIR 3 in UPSC CSE 2023, calls Virat Kohli her inspiration, says…
Donuru Ananya Reddy, who secured AIR 3 in UPSC CSE 2023, calls Virat Kohli her inspiration, says…![submenu-img]() Nestle getting children addicted to sugar, Cerelac contains 3 grams of sugar per serving in India but not in…
Nestle getting children addicted to sugar, Cerelac contains 3 grams of sugar per serving in India but not in…![submenu-img]() Viral video: Woman enters crowded Delhi bus wearing bikini, makes obscene gesture at passenger, watch
Viral video: Woman enters crowded Delhi bus wearing bikini, makes obscene gesture at passenger, watch![submenu-img]() This Swiss Alps wedding outshine Mukesh Ambani's son Anant Ambani's Jamnagar pre-wedding gala
This Swiss Alps wedding outshine Mukesh Ambani's son Anant Ambani's Jamnagar pre-wedding gala


































)
)




)
)
)
)
)
)