The government of India wants to promote domestic manufacturers of telecom products as it is worried that foreign suppliers of telecom equipment might indulge in cyber espionage during a crisis or war.
The government of India wants to promote domestic manufacturers of telecom products as it is worried that foreign suppliers of telecom equipment, especially China, might indulge in cyber espionage during a crisis or war.
The department of telecom (DoT) under the ministry of communication and information technology has chalked out an elaborate policy and will soon come out with a notification. If all goes as planned, foreign firms like Chinese telecom giant Huawei will be wiped out from the Indian market.
Telecom department documents, accessed by DNA, talk of “heightened security risk” as the primary reason behind promoting ‘made in India’ products. The documents say that during war, an enemy country can control or instruct its suppliers to block equipment supply or critical support. “Some countries have the means, opportunity and motive to use their telecom companies for malicious purpose to shutdown or degrade India’s critical national security systems in time of crisis or war,” the DoT notes.
At present, the Indian telecom sector depends heavily on foreign companies for equipment as well as maintenance.
The department has identified 18 hardware items used for telecommunications that will be put under a preferential market access category and that will be manufactured locally. They include SIM cards, base stations switching centres, network management systems, modems used for WiFi or 3G broadband services and EPABX boxes. The new rules are expected to come into force from April 1, 2013.
Though the government wants to achieve 100% dependence on domestic manufacturers, the shift will take place gradually. It will first be mandatory for all telecom companies to procure a minimum of 30% equipment from domestic manufacturers in the first year. This will go up to 45% by 2017 and so on.
“In the context of emerging cyber attacks, the security of the telecommunication infrastructure and network elements such as routers, switches, exchanges, transmission systems and other telecom infrastructure elements, is of paramount importance,” say the documents.
Threats cannot be ruled out “as the entire supply chain associated with hardware and software, including managed services, can be easily used to insert features or vulnerabilities into any product that could assist espionage and cyber warfare”.
Experts say post-production evaluation processes at present “may not necessarily be designed to uncover malicious codes”. “The evaluation programmes may only create a false sense of security that an incomplete, flawed, or misapplied evaluation would provide. And this may result in unwittingly dropping the guard simply because an accredited expert has approved the product,” one expert said.
![submenu-img]() Meet Gautam Adani’s ‘right hand’, used to work as teacher, he’s now Rs 1600000 crore…
Meet Gautam Adani’s ‘right hand’, used to work as teacher, he’s now Rs 1600000 crore…![submenu-img]() Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..
Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..![submenu-img]() Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...
Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...![submenu-img]() This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..
This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..![submenu-img]() Volkswagen Taigun GT Line, Taigun GT Plus launched in India, price starts at Rs 14.08 lakh
Volkswagen Taigun GT Line, Taigun GT Plus launched in India, price starts at Rs 14.08 lakh![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
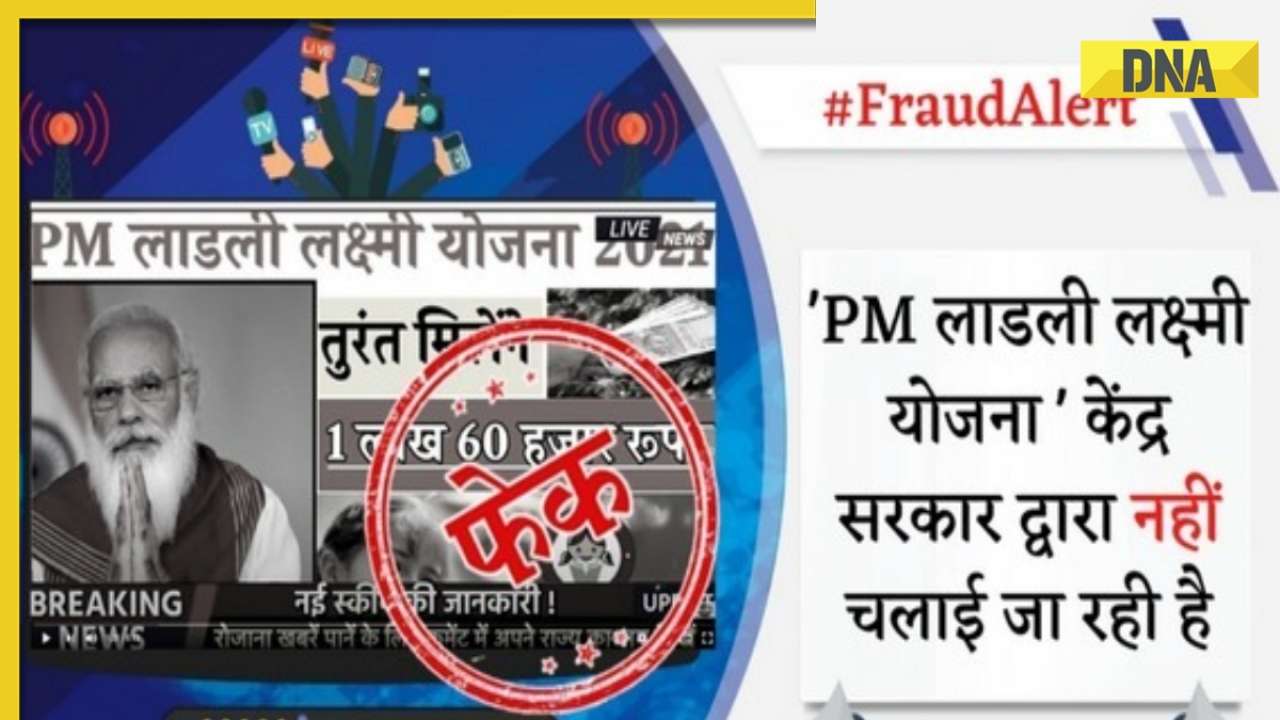
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..
Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..![submenu-img]() Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now
Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now![submenu-img]() Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..
Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..![submenu-img]() In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding
In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding![submenu-img]() In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month
In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles
DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles![submenu-img]() Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..
Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..![submenu-img]() Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...
Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...![submenu-img]() This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..
This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..![submenu-img]() Mumtaz urges to lift ban on Pakistani artistes in Bollywood: ‘Woh log hum logon se...'
Mumtaz urges to lift ban on Pakistani artistes in Bollywood: ‘Woh log hum logon se...'![submenu-img]() Not Kiara Advani, but this actress was first choice opposite Shahid Kapoor in Kabir Singh, she rejected because...
Not Kiara Advani, but this actress was first choice opposite Shahid Kapoor in Kabir Singh, she rejected because...![submenu-img]() IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians
IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians![submenu-img]() IPL 2024: How can RCB still qualify for playoffs after 1-run loss against KKR?
IPL 2024: How can RCB still qualify for playoffs after 1-run loss against KKR?![submenu-img]() CSK vs LSG, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
CSK vs LSG, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() RR vs MI: Yuzvendra Chahal scripts history, becomes first bowler to achieve this massive milestone in IPL
RR vs MI: Yuzvendra Chahal scripts history, becomes first bowler to achieve this massive milestone in IPL![submenu-img]() 'Yeh toh second tier ki bhi team nhi': Ramiz Raja slams Babar Azam and co. after 3rd T20I loss vs New Zealand
'Yeh toh second tier ki bhi team nhi': Ramiz Raja slams Babar Azam and co. after 3rd T20I loss vs New Zealand![submenu-img]() Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…
Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…![submenu-img]() India's most expensive wedding costs more than weddings of Isha Ambani, Akash Ambani, total money spent was...
India's most expensive wedding costs more than weddings of Isha Ambani, Akash Ambani, total money spent was...![submenu-img]() Meet Indian genius who lost his father at 12, studied at Cambridge, took Rs 1 salary, he is called 'architect of...'
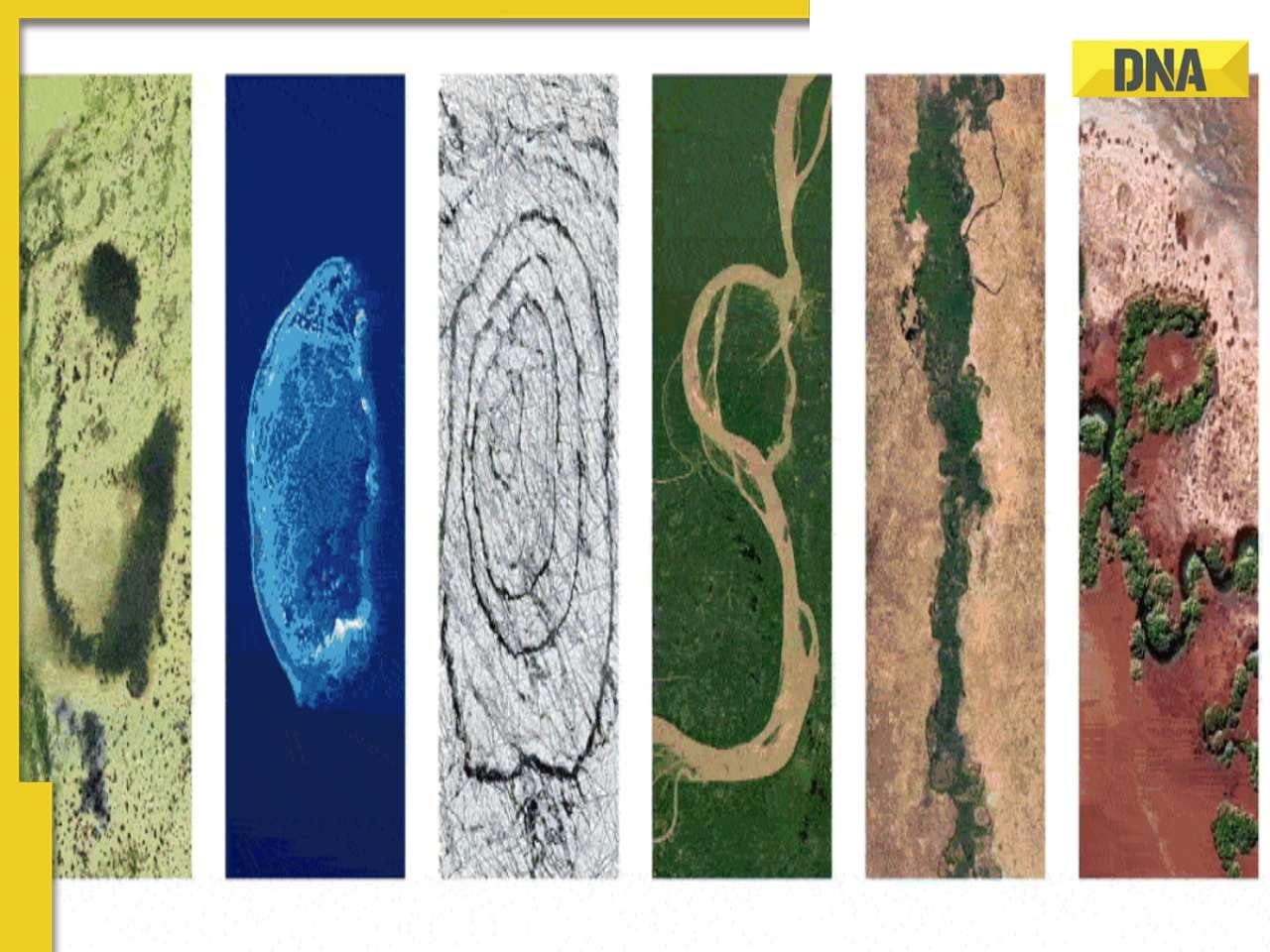
Meet Indian genius who lost his father at 12, studied at Cambridge, took Rs 1 salary, he is called 'architect of...'![submenu-img]() Earth Day 2024: Google Doodle features aerial photos of planet's natural beauty, biodiversity
Earth Day 2024: Google Doodle features aerial photos of planet's natural beauty, biodiversity![submenu-img]() Meet India's first billionaire, much richer than Mukesh Ambani, Adani, Ratan Tata, but was called miser due to...
Meet India's first billionaire, much richer than Mukesh Ambani, Adani, Ratan Tata, but was called miser due to...



































)
)
)
)
)
)