When we talk about computers, smartphones, tablets or mobiles, we generally assume that there's just one operating system. We believe that it is the interface between humans and hardware. But what if there is more than one OS?
In fact, there is a secret second operating system — the baseband OS. And this could make every mobile phone insecure because every time you send a text message or receive a call, the baseband OS registers it. The problem with this OS is that it is usually proprietary, closed-source, bug-ridden, and has extensive hardware level access to your data.
A phone's baseband is like a black box that communicates with a cell tower and has hardware level access to your GPS and microphone. The baseband is firmly established in your phone hardware and is difficult or unlikely to change. It has its own CPU and is vulnerable to attacks. The Blackphone or any other mobile phone for that matter does not protect against this.
Researchers from across the world are looking into the possibilities of baseband hacking. Mobile baseband can be hacked using a fake base station. A hacker will route all your mobile phone data via this fake base station and eavesdrop on all conversations and go through all data, be it text or audio or video.
After copying all your data, the hacker can communicate with another real station to complete the network connection. All this goes on without the user realising that he/she has been spied upon. Even the most secure phones are vulnerable to such attacks.
A base station is usually a 30-ft tower. A London firm, PA Consulting, figured out how to shrink the entire thing into a 3-inch Raspberry Pi, one of the biggest inventions in recent years. This $30 Linux-based computer, about the size of a credit card, is targeted at educating the next generation of software and hardware engineers in programming.
"The Raspberry Pi base station that was developed at our Cambridge Technology Centre shows the vast potential of low-cost hardware. Such small cell technologies open up several possibilities — simple in-home coverage improvement, replacement networks in disaster areas, provision of targeted advertising, or even "dial-an-exhibit" at a tourist location," Frazer Bennett, technology expert, PA Consulting Group, told dna.
A base station being run on a 3-inch Raspberry Pi makes baseband hacking a significant threat. It is still to be seen how secure smart phone manufacturers such as BlackBerry, Boeing, GeeksPhone and Silent Circle deal with this.
![submenu-img]() Meet Isha Ambani's lesser-known relative who owns Rs 6368 crore business, Mukesh Ambani is his...
Meet Isha Ambani's lesser-known relative who owns Rs 6368 crore business, Mukesh Ambani is his...![submenu-img]() India gets a new supercar with 325 km/h top speed, priced at Rs 3.99 crore, it is made by…
India gets a new supercar with 325 km/h top speed, priced at Rs 3.99 crore, it is made by…![submenu-img]() Akash Ambani led Reliance Jio creates a new record, it is now world’s largest…
Akash Ambani led Reliance Jio creates a new record, it is now world’s largest…![submenu-img]() Hema Malini reveals Dharmendra was against her political career: ‘He told me…’
Hema Malini reveals Dharmendra was against her political career: ‘He told me…’ ![submenu-img]() US Congress passes Ukraine, Israel foreign aid bill worth $95 billion
US Congress passes Ukraine, Israel foreign aid bill worth $95 billion![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
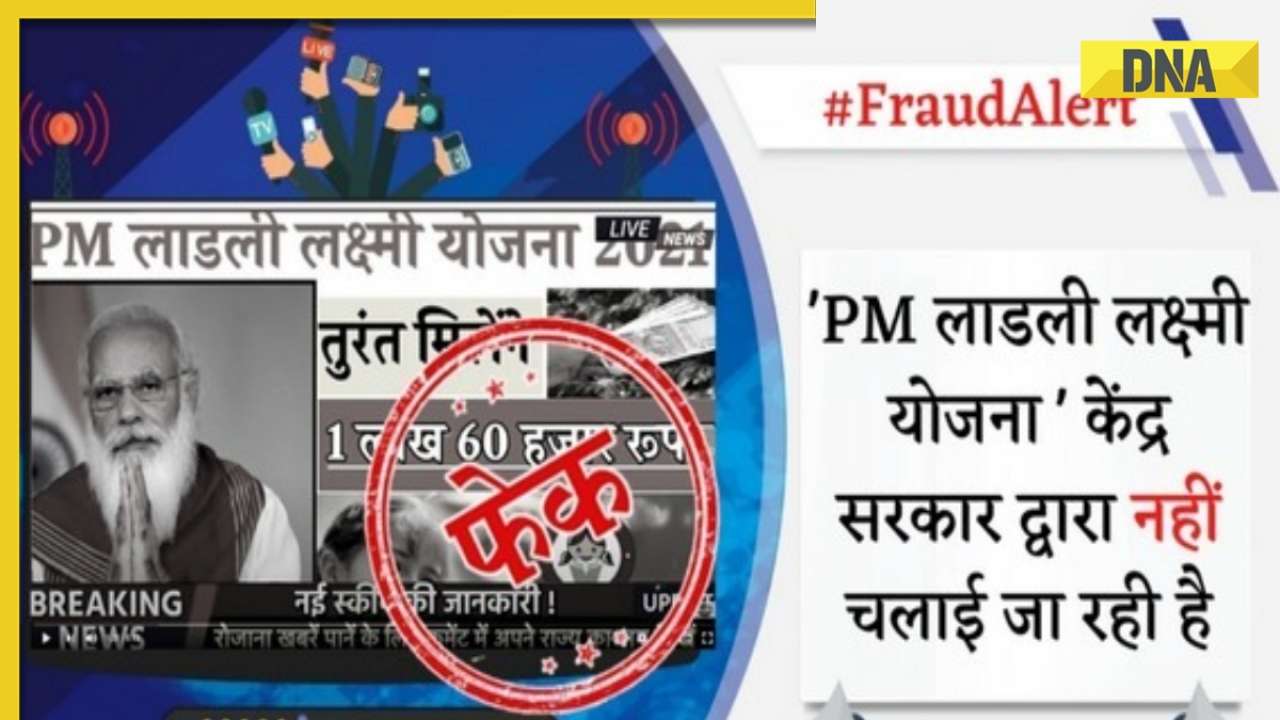
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() Streaming This Week: Crakk, Tillu Square, Ranneeti, Dil Dosti Dilemma, latest OTT releases to binge-watch
Streaming This Week: Crakk, Tillu Square, Ranneeti, Dil Dosti Dilemma, latest OTT releases to binge-watch![submenu-img]() From Salman Khan to Shah Rukh Khan: Actors who de-aged for films before Amitabh Bachchan in Kalki 2898 AD
From Salman Khan to Shah Rukh Khan: Actors who de-aged for films before Amitabh Bachchan in Kalki 2898 AD![submenu-img]() Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..
Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..![submenu-img]() Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now
Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now![submenu-img]() Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..
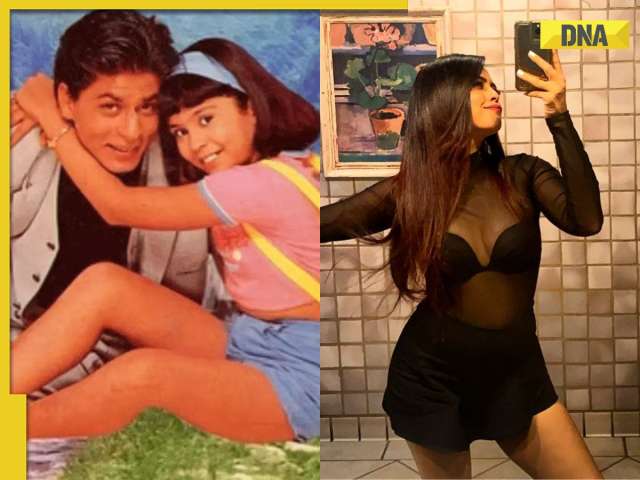
Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles
DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles![submenu-img]() Hema Malini reveals Dharmendra was against her political career: ‘He told me…’
Hema Malini reveals Dharmendra was against her political career: ‘He told me…’ ![submenu-img]() Meet diva sister of Bollywood star, who served as lieutenant in Indian Army; she is now working as...
Meet diva sister of Bollywood star, who served as lieutenant in Indian Army; she is now working as...![submenu-img]() Meet actor, who worked as background dancer, once had only Rs 20 in pocket; now earns Rs 10 crore per film, is worth...
Meet actor, who worked as background dancer, once had only Rs 20 in pocket; now earns Rs 10 crore per film, is worth...![submenu-img]() Ranveer Singh's biggest flop suffered Rs 90-crore loss, faced several delays, was remake of 80s' classic, earned only...
Ranveer Singh's biggest flop suffered Rs 90-crore loss, faced several delays, was remake of 80s' classic, earned only...![submenu-img]() Fahadh Faasil shares how Malayalam cinema's business model is different: 'Unlike the rest of India...'
Fahadh Faasil shares how Malayalam cinema's business model is different: 'Unlike the rest of India...'![submenu-img]() IPL 2024: Marcus Stoinis' century power LSG to 6-wicket win over CSK
IPL 2024: Marcus Stoinis' century power LSG to 6-wicket win over CSK![submenu-img]() DC vs GT, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
DC vs GT, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() DC vs GT IPL 2024 Dream11 prediction: Fantasy cricket tips for Delhi Capitals vs Gujarat Titans
DC vs GT IPL 2024 Dream11 prediction: Fantasy cricket tips for Delhi Capitals vs Gujarat Titans ![submenu-img]() IPL 2024: How can MI still qualify for playoffs after 9-wicket loss against RR?
IPL 2024: How can MI still qualify for playoffs after 9-wicket loss against RR?![submenu-img]() IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians
IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians![submenu-img]() This city to witness 'Zero Shadow Day' today; know everything about this rare celestial event
This city to witness 'Zero Shadow Day' today; know everything about this rare celestial event![submenu-img]() Woman diagnosed with 'love brain' after calling boyfriend 100 times daily, details inside
Woman diagnosed with 'love brain' after calling boyfriend 100 times daily, details inside![submenu-img]() Puppy reunites with mother after being stuck inside shop, viral video wins internet
Puppy reunites with mother after being stuck inside shop, viral video wins internet![submenu-img]() Meet man, an Indian, who made changes in his super expensive Rolls Royce for comfort of his...
Meet man, an Indian, who made changes in his super expensive Rolls Royce for comfort of his...![submenu-img]() Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…
Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…





































)
)
)
)
)
)