If not for the NTRO’s timely intervention, many of these attacks would have succeeded and created havoc in India’s massive security architecture.
On November 15, 2010, the additional secretary in the ministry of finance received an email with an attachment from the Indian high commissioner in Islamabad, Pakistan.
The attachment, unknown to the mail’s sender and the recipient, was a cyber attack carrying a malware designed to hack into as many systems as possible.
As investigators from the National Technical Research Organisation (NTRO), India’s technical intelligence agency, began their investigations, they learnt that the high commissioner was not even aware about the mail. It had an excel sheet as attachment, titled “G-20services.xls”.
Foreign secretary Nirupama Rao was one of the recipients among a host of other senior officials. As soon as they opened the attachment, the malware downloaded itself and began to spread through the system, creating ghost commands that would begin transmitting information to the attacker.
Had it not been for the NTRO’s timely intervention, many of these attacks would have succeeded and created havoc in India’s massive security architecture causing an incalculable loss of sensitive information.
Beginning in 2009, the number of cyber attacks on India’s vital systems has risen sharply in quality and quantity. Investigators have concluded that this kind of selective targeting of key senior departments, like the July 12, 2011, attack on the PMO, can only be done by a state-sponsored agency.
But finding the real culprit is not easy. Officials familiar with several such investigations told DNA that the actual attacker is rarely known or traced. They use third party protocols as fronts to launch an attack, direct the information stored on the victim’s computer towards a secret website that serve as a “drop box”, from where the information can be recovered.
Conventional wisdom said most of the attacks were from China until the investigators made a stunning discovery. Written into the code of the malwares were Chinese characters that immediately confirmed their initial suspicion. But working on a hunch, they removed the Chinese characters and discovered that the malware was still working at peak efficiency. “Obviously this was a red herring meant to mislead us,” a senior official said.
While there is little doubt that many of these attacks could emanate from China, investigators are also convinced that an ally in the West could be behind some of these cyber espionage operations.
The ingenuity and range of some of the cyber attacks has left investigators astounded. In one case they found a whole sub domain created under the government-owned National Informatics Centre (NIC).The NIC operates the backbone of the government’s IT platform and it was shocking to find a fake sub domain called www.indexnews.indmin.net registered with NIC operating without raising any alarm.
In another case, a mail was sent out from the official id of an IPS official, Pranab Ray, in the home ministry. The only problem with the mail was the id — pranabray@nic.in — was sent long after Ray had retired from service. Once again, the mail had an attachment with malwares that could hack into sensitive systems and pry information out.
But the most stunning attack happened when the NTRO detected that information from computers not even linked to the internet was leaking out. These were secret e-grams, sent over secure networks carrying sensitive diplomatic communiqués to India from its embassies abroad.
An elaborate investigation led them to an Indian Foreign Service officer working as a director in the ministry of external affairs’ Western Europe desk. At some point, her computer had been infected with a unique malware that worked only on pen drives or removable storage disks.
Once it lodged itself on a pen drive, it would wait till it was connected to a standalone computer with sensitive data. The malware would then deploy from the pen drive, pick up all sensitive folders and return to the pen drive. As soon as it was connected to a computer with an internet connection, it would immediately download all the sensitive files and transmit them to the attacker.
In cyber espionage terms, this operation is described as “bridging the air-gap”. Such expertise, investigators concluded, could only come from a hostile state with tremendous cyber capabilities.
![submenu-img]() Meet Gautam Adani’s ‘right hand’, used to work as teacher, he’s now Rs 1600000 crore…
Meet Gautam Adani’s ‘right hand’, used to work as teacher, he’s now Rs 1600000 crore…![submenu-img]() Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..
Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..![submenu-img]() Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...
Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...![submenu-img]() This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..
This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..![submenu-img]() Volkswagen Taigun GT Line, Taigun GT Plus launched in India, price starts at Rs 14.08 lakh
Volkswagen Taigun GT Line, Taigun GT Plus launched in India, price starts at Rs 14.08 lakh![submenu-img]() DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'
DNA Verified: Is CAA an anti-Muslim law? Centre terms news report as 'misleading'![submenu-img]() DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message
DNA Verified: Lok Sabha Elections 2024 to be held on April 19? Know truth behind viral message![submenu-img]() DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here
DNA Verified: Modi govt giving students free laptops under 'One Student One Laptop' scheme? Know truth here![submenu-img]() DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar
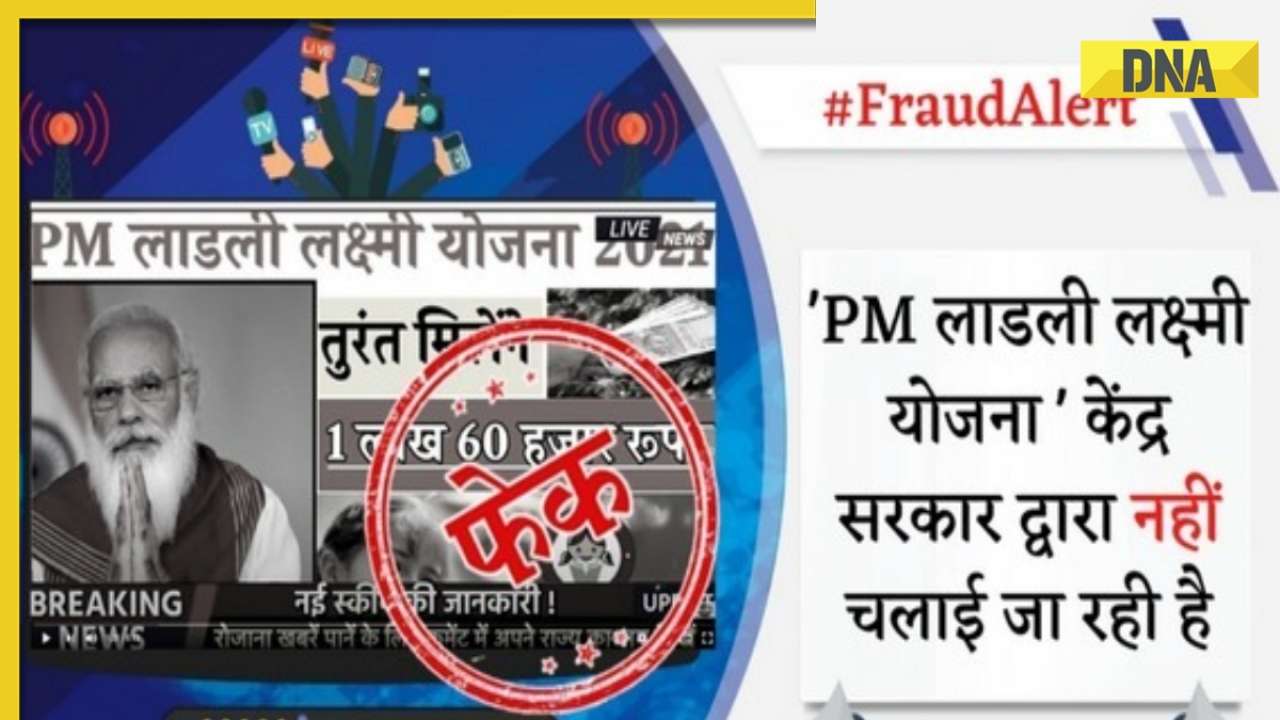
DNA Verified: Shah Rukh Khan denies reports of his role in release of India's naval officers from Qatar![submenu-img]() DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth
DNA Verified: Is govt providing Rs 1.6 lakh benefit to girls under PM Ladli Laxmi Yojana? Know truth![submenu-img]() Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..
Remember Abhishek Sharma? Hrithik Roshan's brother from Kaho Naa Pyaar Hai has become TV star, is married to..![submenu-img]() Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now
Remember Ali Haji? Aamir Khan, Kajol's son in Fanaa, who is now director, writer; here's how charming he looks now![submenu-img]() Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..
Remember Sana Saeed? SRK's daughter in Kuch Kuch Hota Hai, here's how she looks after 26 years, she's dating..![submenu-img]() In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding
In pics: Rajinikanth, Kamal Haasan, Mani Ratnam, Suriya attend S Shankar's daughter Aishwarya's star-studded wedding![submenu-img]() In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month
In pics: Sanya Malhotra attends opening of school for neurodivergent individuals to mark World Autism Month![submenu-img]() DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?
DNA Explainer: What is cloud seeding which is blamed for wreaking havoc in Dubai?![submenu-img]() DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?
DNA Explainer: What is Israel's Arrow-3 defence system used to intercept Iran's missile attack?![submenu-img]() DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence
DNA Explainer: How Iranian projectiles failed to breach iron-clad Israeli air defence![submenu-img]() DNA Explainer: What is India's stand amid Iran-Israel conflict?
DNA Explainer: What is India's stand amid Iran-Israel conflict?![submenu-img]() DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles
DNA Explainer: Why Iran attacked Israel with hundreds of drones, missiles![submenu-img]() Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..
Meet actor who worked with Amitabh Bachchan, Aishwarya Rai, entered films because of a bus conductor, is now India's..![submenu-img]() Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...
Meet Bollywood star, who was a tourist guide, married 4 times, went bankrupt, his son died by suicide, then...![submenu-img]() This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..
This actor made Sharmila Tagore forget her lines, once did film for Rs 100, could never be a superstar because..![submenu-img]() Mumtaz urges to lift ban on Pakistani artistes in Bollywood: ‘Woh log hum logon se...'
Mumtaz urges to lift ban on Pakistani artistes in Bollywood: ‘Woh log hum logon se...'![submenu-img]() Not Kiara Advani, but this actress was first choice opposite Shahid Kapoor in Kabir Singh, she rejected because...
Not Kiara Advani, but this actress was first choice opposite Shahid Kapoor in Kabir Singh, she rejected because...![submenu-img]() IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians
IPL 2024: Yashasvi Jaiswal, Sandeep Sharma guide Rajasthan Royals to 9-wicket win over Mumbai Indians![submenu-img]() IPL 2024: How can RCB still qualify for playoffs after 1-run loss against KKR?
IPL 2024: How can RCB still qualify for playoffs after 1-run loss against KKR?![submenu-img]() CSK vs LSG, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report
CSK vs LSG, IPL 2024: Predicted playing XI, live streaming details, weather and pitch report![submenu-img]() RR vs MI: Yuzvendra Chahal scripts history, becomes first bowler to achieve this massive milestone in IPL
RR vs MI: Yuzvendra Chahal scripts history, becomes first bowler to achieve this massive milestone in IPL![submenu-img]() 'Yeh toh second tier ki bhi team nhi': Ramiz Raja slams Babar Azam and co. after 3rd T20I loss vs New Zealand
'Yeh toh second tier ki bhi team nhi': Ramiz Raja slams Babar Azam and co. after 3rd T20I loss vs New Zealand![submenu-img]() Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…
Mukesh Ambani's son Anant Ambani likely to get married to Radhika Merchant in July at…![submenu-img]() India's most expensive wedding costs more than weddings of Isha Ambani, Akash Ambani, total money spent was...
India's most expensive wedding costs more than weddings of Isha Ambani, Akash Ambani, total money spent was...![submenu-img]() Meet Indian genius who lost his father at 12, studied at Cambridge, took Rs 1 salary, he is called 'architect of...'
Meet Indian genius who lost his father at 12, studied at Cambridge, took Rs 1 salary, he is called 'architect of...'![submenu-img]() Earth Day 2024: Google Doodle features aerial photos of planet's natural beauty, biodiversity
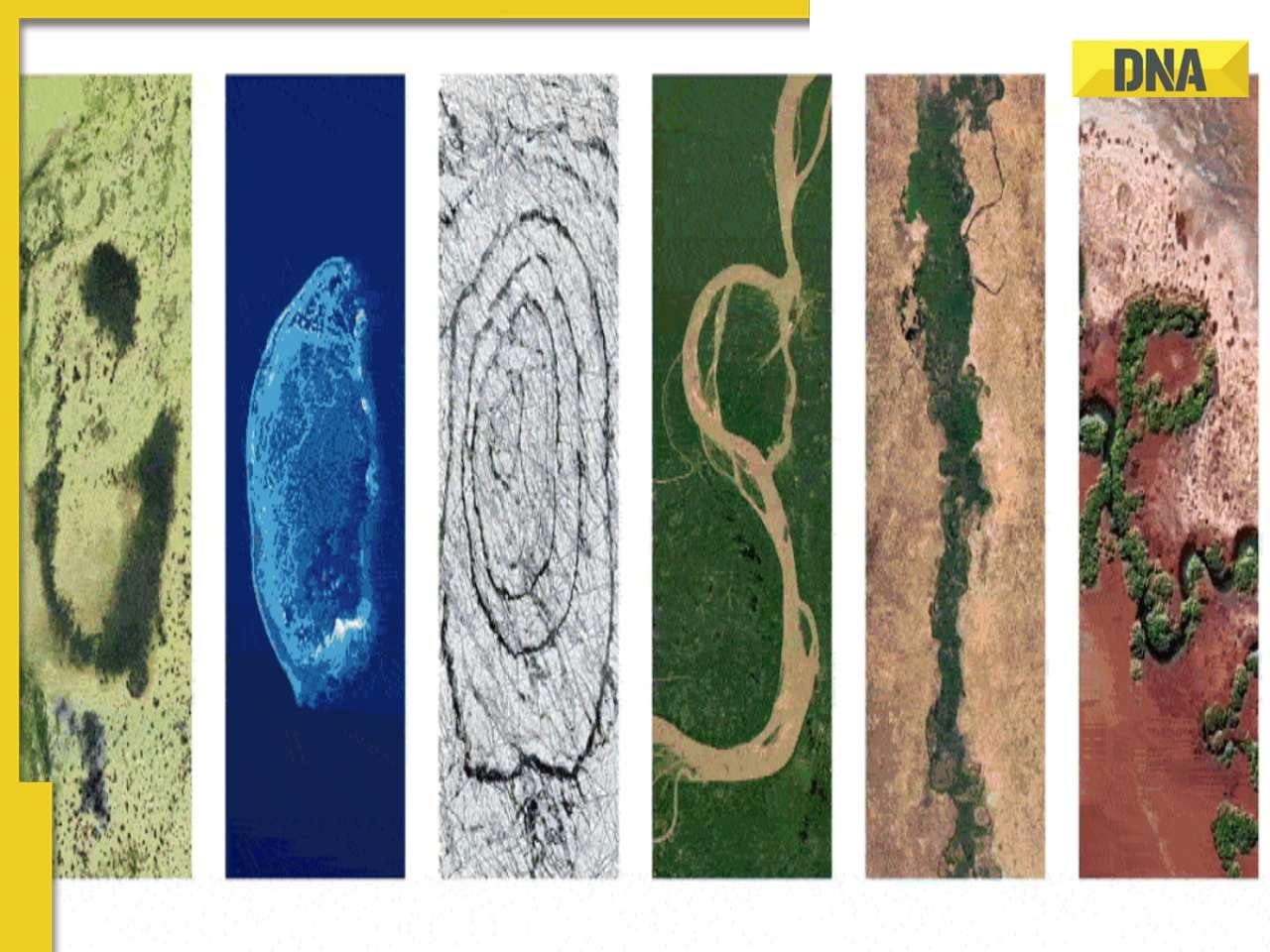
Earth Day 2024: Google Doodle features aerial photos of planet's natural beauty, biodiversity![submenu-img]() Meet India's first billionaire, much richer than Mukesh Ambani, Adani, Ratan Tata, but was called miser due to...
Meet India's first billionaire, much richer than Mukesh Ambani, Adani, Ratan Tata, but was called miser due to...


































)
)
)
)
)
)